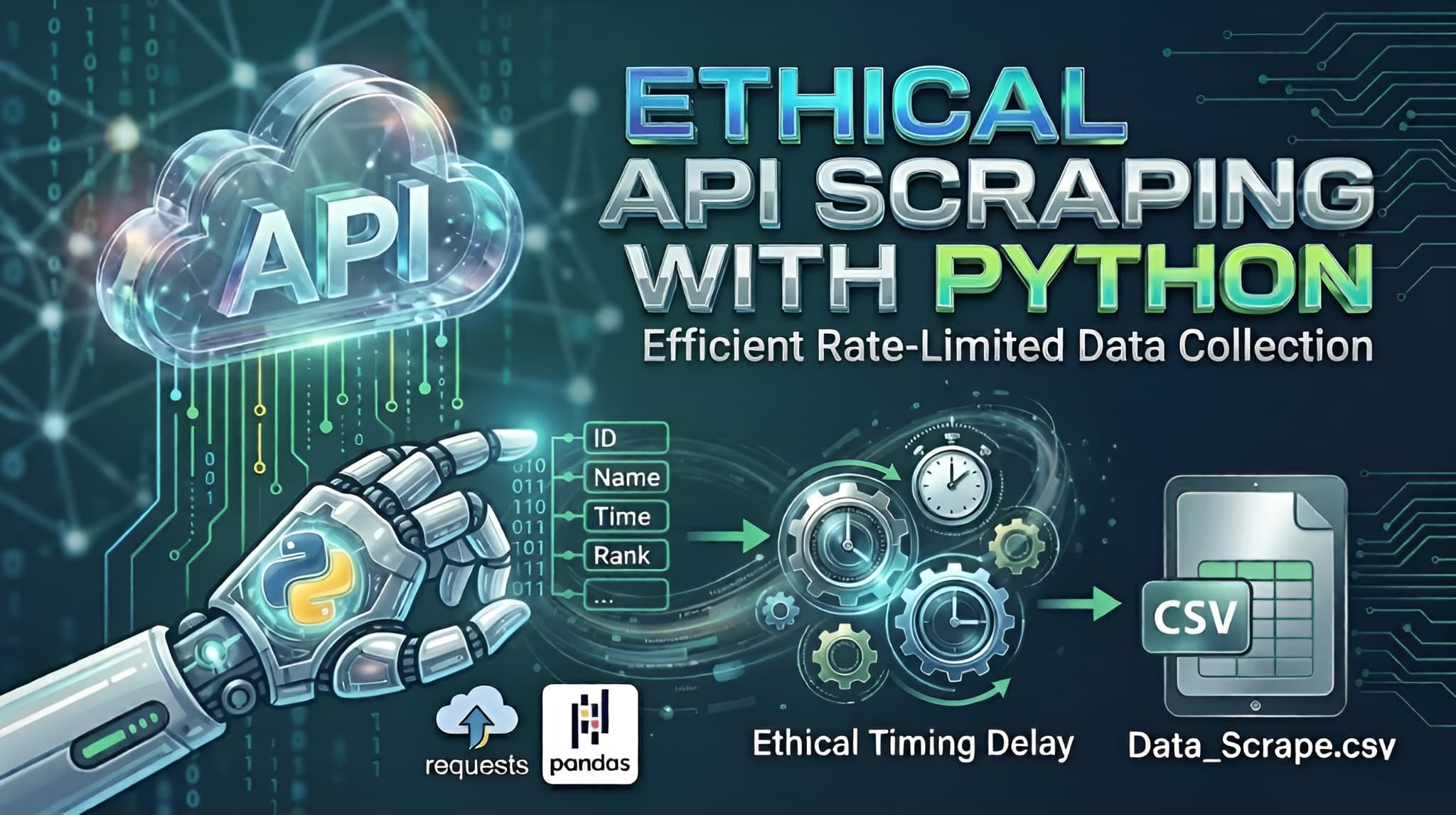
Efficient & Ethical: How to Scrape API Data Continuously Using Python
In the world of data science, the data you need isn't always available in a neat, downloadable package. Often, it sits behind an API that requires individual queries for every piece of information.If you try to "blast" an API with thousands of requests per second, you’ll likely trigger a DDoS (Distributed Denial of Service) protection system, resulting in a blocked IP or a banned account. Today, we’ll walk through a professional Python template designed to fetch data sequentially, respect server limits, and save the results into a clean CSV file.The Strategy: "Slow and Steady Wins the Race"When scraping an API, we want to mimic human behavior. Our script follows three golden rules:Iterative Logic: Loop through a range of IDs (or "Bib numbers" in this case).Defensive Timing: Introduce a random delay between requests.Graceful Error Handling: Ensure one failed request doesn't crash the whole script.The Python ImplementationBelow is the generalized template. Notice how we use the requests library for communication and pandas for data organization.Python Code Snippet:import requestsimport jsonimport timeimport randomimport pandas as pd# --- 1. Configuration ---# Use placeholders for sensitive informationAPI_URL = "https://api.example.com/v1/search"HEADERS = { 'accept': 'application/json', 'apikey': 'YOUR_API_KEY_HERE', # Keep your keys private! 'user-agent': 'DataCollector/1.0'}# Define the range of data you want to fetchSTART_ID = 10001END_ID = 11000OUTPUT_FILE = "collected_data.csv"all_data = []print(f"Starting data fetch from ID {START_ID} to {END_ID}...")# --- 2. The Request Loop ---for current_id in range(START_ID, END_ID + 1): payload = {"id": str(current_id)} try: # Sending the POST request response = requests.post(API_URL, headers=HEADERS, json=payload) if response.status_code == 200: result = response.json() # Check if the data key exists and has content if result.get("status") and result.get("data"): for entry in result["data"]: # Flatten the JSON response into a clean dictionary record = { "id": current_id, "name": entry.get("name"), "category": entry.get("category"), "rank": entry.get("rank"), # Add or remove fields as per your API response } all_data.append(record) print(f"Success: ID {current_id}") else: print(f"No data found for ID {current_id}") else: print(f"Error {response.status_code} for ID {current_id}") except Exception as e: print(f"Failed to fetch ID {current_id}: {e}") # --- 3. The Anti-Blocking Mechanism --- # We use a random delay to prevent being flagged as a bot/DoS attack wait_time = random.uniform(1.0, 3.0) time.sleep(wait_time)# --- 4. Data Storage ---if all_data: df = pd.DataFrame(all_data) df.to_csv(OUTPUT_FILE, index=False) print(f"\nTask complete! Data saved to {OUTPUT_FILE}")else: print("\nNo data was collected.")Deep Dive: Why This Works1. Randomized Delays (The time.sleep Trick)Most security systems look for "rhythmic" behavior (e.g., a request exactly every 0.5 seconds). By using random.uniform(1.0, 3.0), the interval between requests is always different. This makes your script look less like a bot and more like an organic user.2. The Power of HeadersIn the HEADERS dictionary, we include a user-agent. This tells the server what "browser" is visiting. Without this, some APIs block requests because they see them as "unidentified scripts."3. Data Flattening with PandasAPIs often return deeply nested JSON. By extracting only the fields we need (like name and rank) and putting them into a list of dictionaries, we make it incredibly easy for Pandas to convert that list into a structured table (CSV).4. Safety FirstThe try...except block is your safety net. If your internet flickers or the server hiccups, the script won't stop; it will simply log the error and move on to the next ID.ConclusionAutomating data collection is a superpower for any developer or analyst. By using this template, you can gather thousands of records while staying on the "good side" of the API providers. Just remember: always check a website’s robots.txt or Terms of Service before you start scraping!